Cyber TSCM
Cyber Technical Surveillance Countermeasures
WHAT IS CYBER TSCM?

Cyber TSCM also includes detection of spyware, malware and malicious payloads via software installed on the devices &/or networks. As well, it includes detection of hybrid eavesdropping devices.
ComSec LLC was the first privately owned counterespionage company to be published as identifying the need for “CYBER TSCM.” More specifically, ComSec identified Cyber TSCM as a more accurate depiction of the best level of TSCM service to address emerging cyber and hybrid technical surveillance threats.
Why Is Cyber TSCM Important?
Securing information and managing cyber risk in an increasingly connected, data driven world is critical. Data is continually created, transferred or stored on devices and/or on networks. Without the proper security, an eavesdropper can exploit the networks, devices and/or connections to steal valuable data and/or compromise privacy. Smartphones, remote cloud data storage, wi-fi camera systems, remote access security apps, smart assistants (e.g. Alexa), BYOD to work, GSM and hybrid bugging devices, etc. add complexity to the task of protecting confidential and/or private information. The appropriate technical security measures for detection and prevention of these threats must be implemented. ComSec LLC’s Cyber TSCM services address this need.
What is the Difference Between TSCM and Cyber TSCM?
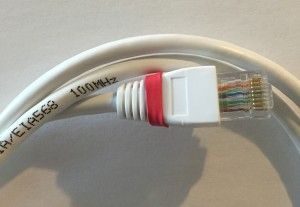
TSCM is an acronym for Technical Surveillance Countermeasures. TSCM involves detecting traditional electronic eavesdropping devices. These are devices that generally require an eavesdropper, or their accomplice(s), to physically recover the device to access the collected information. TSCM also includes physical wire tapping where the eavesdropper can access the information from the tap location along the line. Ultimately, this means that an eavesdropper faces a high risk of detection when installing the device and/or when recovering the eavesdropping device(s) from the collection site.

Contact ComSec today or call +1.800.615.0392 to discuss your organizations Cyber TSCM requirements.
Why Is Cyber TSCM Such an Important Element of a Cybersecurity Program?
The personnel who maintain the cybersecurity program are trained to detect network threats. They are not trained, or equipped, to detect eavesdropping devices. As well, eavesdropping exploitations of the cellular network or use of hybrid eavesdropping devices are not within their area of expertise. If your cybersecurity program does not include Cyber TSCM, you could be missing a very credible threat. For instance, eavesdropping devices can be used to push data out over the cellular network. And, hybrid eavesdropping devices can be disguised as harmless data cables. The results of these types of eavesdropping attacks can just as devastating as an IT related cybersecurity issue.
ComSec’s Cyber TSCM Inspection detects electronic eavesdropping devices and/or technical intrusions via remote access attack. These attacks are conducted via GSM, 3G & 4G, and provide remote cellular access and collection of your confidential information. Cyber intruders use these attacks to gain unauthorized access (from anywhere in the world) to your data via a mobile phone signal. ComSec LLC has an advanced suite of Cyber Counterespionage – Cyber TSCM services designed to detect anomalies associated with GSM, 3G & 4G and Advanced Persistent Threats (APT) attacks.
What are Hybrid Devices?
Hybrid devices are devices that are commonly found in offices or homes which have been re-purposed as eavesdropping devices. So, while the device would not be suspect because of its appearance and/or location, it is actually a very credible threat that can only be detected through use of Cyber TSCM methods.
ComSec LLC’s Cyber TSCM Inspections
ComSec LLC’s Cyber Technical Surveillance Counter Measures (Cyber TSCM) inspections are globally unique in that we use unique equipment and processes. ComSec is uniquely positioned to provide clients with preeminent Cyber TSCM Counter Measures Services. Our Cyber TSCM Services detect active & passive, internal and external threats. These inspections help to protect valuable intellectual property, trade secrets, and proprietary data, financial and other electronically stored private information. Additionally, our Cyber TSCM Inspections protect against advanced persistent threats (APT) and numerous malware variants, and provide of pre-attack intelligence against industrial espionage and “hacktivist” assault.
Our Cyber TSCM Inspections identify exploitable pathways and system entry points that are vulnerable to unauthorized remote system access. ComSec LLC’s unique radio frequency spectrum analysis will also provide a professional evaluation of your business executive offices or facility’s security posture against electronic eavesdropping and GSM / 3G / 4G and CDMA remote cellular attacks. The Cyber TSCM Inspection consists of thorough electronic and physical examinations to detect unauthorized audio, cellular and optical devices (Technical Surveillance Device).
Don’t trust your valuable IP to an antiquated cyber risk management program… Contact ComSec
Interested in CYBER TSCM Training?
ComSec’s CYBER TSCM TRAINING CENTER services USA, GOV, MIL & LE clients. Headquartered in Virginia Beach, Virginia, Our secure facility offers training classes for: CYBER TSCM, COMSEC MOBILE SIGINT KITS, KESTREL TSCM PRO Spectrum Analytics Software, The ORIUS WIFI HUNTER and The PREDATOR RF HUNTER. Contact ComSec about CYBER TSCM TRAINING