Corporate espionage is considered a flourishing underground business, whose devastating effects can be detected all across the United States. According to recent information provided by the FBI on June 28, 2012, it appears that this major problem has affected hundreds of American companies, making hundreds of businessmen lose a grand total of than $13 billion in cases opened only in 2012. This significant loss includes the future market value of stolen trade secrets. Employees and/or former employees play an important active role in the whole corporate espionage issue.
Stimulated by financial incentives, and most likely influenced by these hard, unstable economic times, most employees agree to share confidential information. Companies involved in this unlawful strategy quite often prefer to pay an inside informer rather than investing a greater amount of money in their own legit development. Apparently, it seems that buying stolen information received while relying on electronic eavesdropping is cheaper and easier to attain than a natural and perfectly legal growth.
It’s not very difficult to discover that you’ve become a victim of this major problem called corporate espionage. If you realize that your competition, your staff or the media is revealing information that you consider private, in most of the cases this means that someone has decided to uncover the well-kept secrets of your company by counting on the efficiency of electronic eavesdropping, or bugging.
Can other people prosper by simply paying for your confidential information? If you keep important secrets that are worth a significant amount of money, the answer is yes. Below you will find five of the most frequent ways in which you could endanger your own company, leaving yourself exposed to various corporate espionage techniques:
- Allowing your staff/visitors to bring and use their cell phones inside your company.
- This is perhaps the most common espionage technique that can cost you millions of dollars in losses. Any kind of cell phone can be equipped with a remote activation feature which can be virtually impossible to detect. This way, the eavesdropper can use it to steal your important information, by simply placing the phone in a strategic spot, like a conference room, for example.
- Neglecting the presence of revolutionary tools designed to encourage internal theft.
- Powerful tools launched on the market by recording company 2ReCall, and applications such as VOMIT (Voice Over Misconfigured Internet Telephones), can work to your disadvantage, helping eavesdroppers share your most important information, by tracking and even recording your phone calls. By following this path, your own employees have the opportunity to trace and even sabotage your business deals, future strategies/partnerships, threatening your prosperity and financial status.
- Profiting from contracted office cleaning services without acknowledging the risks.
- Your cleaning staff has unlimited access inside your building. The cleaning people come in late, usually when the rest of your employees are already at home, thus they could easily install a bugging device or use a remote activate cellular device to steal your valuable information without being caught. Moreover, taking into account that they usually endure hardship, they could be easily tricked into uncovering and sharing the well-kept secrets of your company. In this case, the risk of getting caught is outweighed by the promise of financial security.
- Giving various providers free, unsupervised access inside your building.
- Informers often count on a highly effective strategy: they fabricate a service outage and then they use a clever disguise to set foot in your facility and to “solve” your problem. This is why you should always be extremely caution when you are dealing with people claiming they were called to fix your internet connection, air conditioner problems and so on.
- While trying to make you believe that they are fixing the problem, eavesdroppers carefully plant the bugging devices, leaving you exposed to dangerous, costly information leakage. This is why it is extremely important to be able to count on a dedicated, experienced, loyal member of your security team, designated to supervise the provider you’ve decided to let inside your building.
- Failure to comply with efficient IT security measures.
- Important companies spend millions of dollars trying to implement efficient IT security measures, in an attempt to protect their valuable, confidential information. On the other hand, those who want to annihilate interior and exterior factors threatening their privacy and prosperity should be fully aware of the fact that physical security aspects and counter surveillance steps are also essential in preventing corporate espionage. Technical surveillance countermeasure, TSCM, sweeps are as important and efficient as IT security measures. This is why you need to rely on preventive quarterly TSCM – electronic countermeasures will help you protect the secrets of your company, safeguarding your financial status from the devastating effects of industrial espionage.
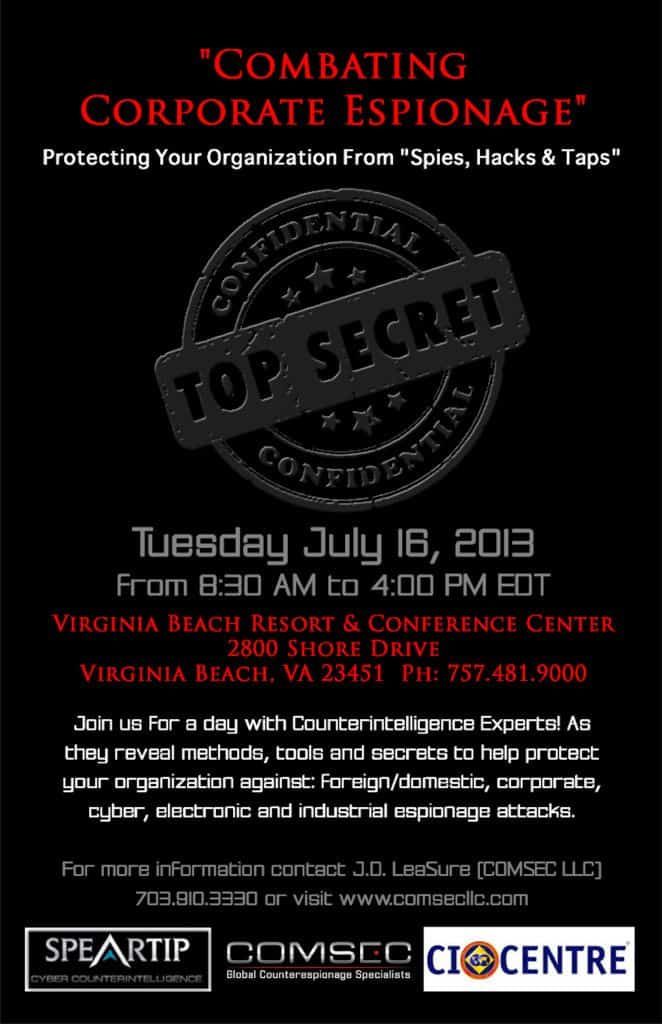
In case you need more accurate info on TSCM, Eavesdropping Detection and Bug Sweep services, simply call: 1-800-615-0392 or Click here for more info, we can help. ~JDL
*Cyber TSCM ™ is a trade mark of ComSec LLC
© 2015 ComSec LLC. All rights reserved.

One comment on “Corporate Espionage: Business Risk Via Electronic Eavesdropping: 5 Tips from Counterespionage Experts”