New IoT Devices Pose Spying Risk
New IoT devices are emerging daily. The growth rate is astonishing. According to Juniper Research, the number of IoT devices in 2021 will reach an eye-opening 46 billion. Wow!
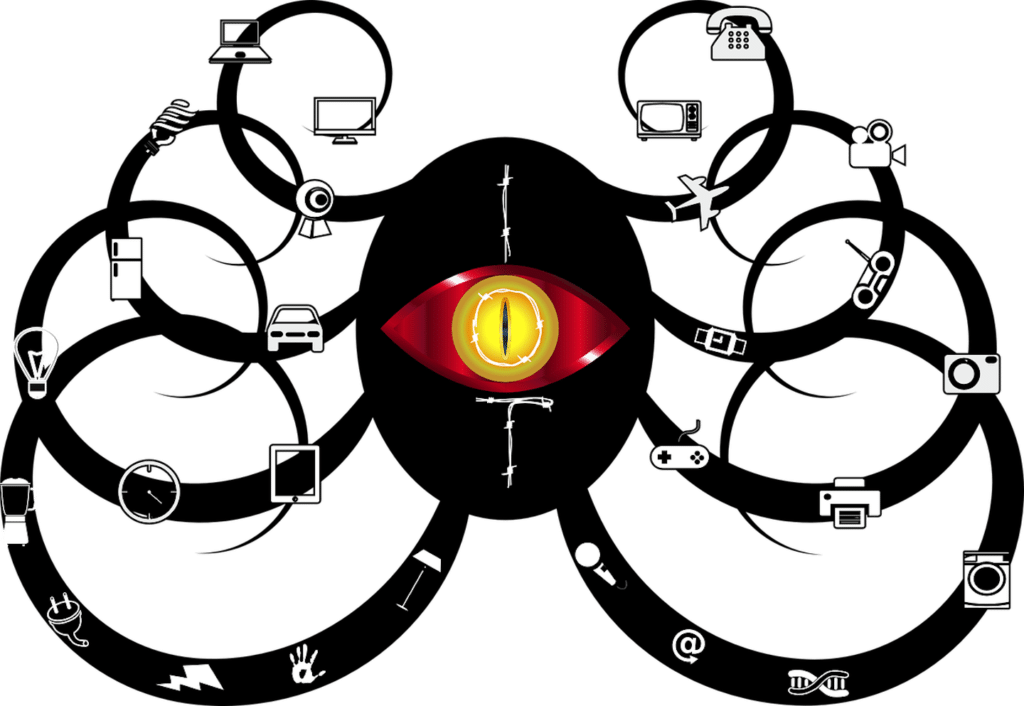
These new IoT devices often make our lives easier. IoT devices can enhance efficiency, convenience, productivity or the overall quality of our lives. But, there is always a trade off between their life enhancing value and a potential loss of privacy. The truth is that many of the convenient IoT devices we use in our home, at work, in the car or wherever we go, also pose spying risks. This is the case with three newly introduced IoT devices.
Apple Air Tag
Description: An IoT device that provides an easy way to keep track of your things. (e.g. wallet, keys, bicycle, etc.)
Features:
- Connects with your Apple device to help locate things you have tagged with the Apple AirTag
- Acts as a beacon by emanating a sound so you can locate your tagged things
- Sends a Bluetooth signal detected by nearby devices in the Find My network and sends the location of the AirTag to iCloud
- It uses Find My network (with 100 million + iPhone, iPad, and Mac devices around the world) to assist with locating your tagged things
- Use Precision Finding with an Apple iPhone 11 or later in conjunction with the Find My app and Siri to find your tagged things
Spying Risk:
- A spy can connect an AirTag to their Apple device and then drop the AirTag in your pocket, handbag, backpack, car, etc. They can track your whereabouts within range of the tag in a 8-24 hour window using their iPhone. The spy can capture your location, your movements, your residence address and your frequently visited places.
- The AirTag can be opened and reprogrammed for malicious purposes. Yes, security researchers hacked the AirTag in less than 10 days.
- If you use an Android device, the only way to find out about the presence of an AirTag nearby is the sound emitted by the Apple AirTag. The sound starts after a period of inactivity (range 8-24 hours). But, if you can’t hear the sound emitted by the AirTag and you are not using an iPhone, the spy can continue tracking you for the AirTag battery life (FYI: it’s about a year.) UPDATE: Tracker Detect APP for Android Now Available from Apple!
Audio Wow+
Description: An IoT device that is a wireless mini microphone with sound effects.
Features:
- Mobile phone direct connected
- Built-in microphone
- Real-time monitoring
- 4 levels of noise reduction
- Cancel and replace original vocals
- Records phone calls and transcribes the content of the caller and receiver separately for easy editing
Spying Risk:
- Can be used for surreptitious recordings since its small size makes it easy to conceal.
- Record both ends of conversation. Most devices only record the half of the conversation where the microphone is present.
- There is a potential for voice recordings to be altered to create records/evidence of conversations that did not occur.
Learn more about the AudioWow+’s capabilities here: https://youtu.be/ZcZFhDgWW6s
Amazon Sidewalk
Description: IoT device that creates a shared “mesh” network of interconnected devices.
Features:
- Creates a low-bandwidth network using Sidewalk Bridge devices
- Shares a portion of your Internet bandwidth to a pool that provides the services to you/your neighbors (maximum bandwidth 80Kbps, 500MB monthly per customer cap. )
- Provided by Amazon at no charge to customers
- Simplifies new device setup
- Extends the low-bandwidth working range of devices like trackers (e.g. Tile)
- Can help devices stay online even when they are out of range of your home Wi-Fi
Spying Risk:
- A spy/hacker connects to the Amazon Sidewalk network, uses malware to penetrate devices and conducts illegal activities with your device.
- A neighbor’s network is not properly secured, but it’s connected to Amazon Sidewalk. A hacker puts ransomware on the neighbor’s network/devices and the ransomeware spreads to other devices connected to the Amazon sidewalk.
- A hacker penetrates a network that is connected to Amazon Sidewalk and and uses it to access information on connected device(s).
You can learn more here about Amazon Sidewalk here: https://youtu.be/jqNqbJ99tGE
ComSec LLC has also previously examined spying risks of the Apple AirPods, the O.M.G cable, etc.
IoT Device Spying Risk
IoT device manufacturers do take measures to protect your privacy. And, the US government is also taking action to protect your privacy. The ‘Internet of Things Cybersecurity Improvement Act of 2020’ was passed in the fall of 2020 by both the US House and Senate. This law sets minimum security standards for Internet of Things devices owned or controlled by the Federal Government, and for other purposes. The law becomes effective in 2022. The National Institute of Standards and Technology (NIST) has subsequently issued four draft guidances to aid with compliance as prescribed in the new law. But, there will always be hackers, spies, and other surreptitious bad actors who will figure out a way to exploit IoT device vulnerabilities for surreptitious purposes.
The Bottom Line
Any IoT device (a device that uses a network to transfer information) poses a spying risk in the hands of bad actors. All it takes is a technical flaw(s) in the network, the software and/or the device. Consumers really need to pay close attention when purchasing and using IoT devices. And, to make sure that their technical security defenses are strong. Consider how the IoT device could be used to spy on you should it be compromised. It’s no doubt that IoT devices can add value to our lives, but there is always a trade off between convenience and privacy. Which is more important to you . . . convenience or privacy?
About the Author:
J.D. LeaSure, CCISM, is the President / CEO of ComSec LLC, a global provider of world class counterespionage and TSCM / Cyber TSCM™ services. www.ComSecLLc.com